Secure communication protocols for distributed AI systems
Secure communication protocols for distributed AI systems

TL;DR:
- Securing distributed AI networks requires multi-layer protocols beyond TLS alone, covering confidentiality, integrity, authentication, and availability.
- Decentralized security models like MLS and WireGuard are preferred for agent fleets due to scalability and resilience.
- Continuous validation, threat modeling, and incorporating zero-trust principles are essential for maintaining security in real-world deployments.
Assuming TLS alone secures your distributed agent network is one of the most common and costly mistakes in modern AI infrastructure design. Real-world deployments of autonomous agent fleets and multi-cloud systems require security at every layer, not just at the transport edge. Teams routinely underestimate zero-trust requirements, skip explicit threat modeling, and misconfigure protocols in ways that create silent vulnerabilities. This guide gives you a clear, practical framework for evaluating and implementing secure communication protocols across distributed, AI-driven networks. Whether you are building agent-to-agent (A2A) pipelines, cross-region orchestration, or secure data streaming, the decisions you make at the protocol level will define your system’s resilience.
Table of Contents
- What are secure communication protocols?
- Centralized vs decentralized security models
- Core secure protocols: TLS 1.3, IPsec, WireGuard, mTLS, and MLS
- Pitfalls, limitations, and real-world deployment challenges
- Zero-trust, blockchain, and the future of agent-to-agent (A2A) security
- A practitioner’s perspective: What most guides miss about protocol security
- How Pilot Protocol helps you implement secure communication at scale
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Definition matters | Secure protocols are more than ciphers-they require layered, explicit rule sets for syntax, semantics, and error handling. |
| Architecture trade-offs | Centralized and decentralized security models offer unique benefits and risks in scaling distributed AI systems. |
| Pick the right protocol | Choose TLS 1.3 for web, WireGuard for throughput, mTLS for mutual auth, and MLS for group communication in agent networks. |
| Watch real-world pitfalls | Misconfigurations, poor key management, and protocol quirks-like firewall blocking or replay attacks-cause most security failures. |
| Future is zero-trust and verifiable IDs | Adopting zero-trust and blockchain/DID-based identity is essential to future-proofing decentralized agent communication. |
What are secure communication protocols?
Before you can choose the right protocol, you need a precise definition. Communication protocols are systems of rules defining syntax, semantics, synchronization, and error recovery for entity communication, layered in models like OSI or TCP/IP for distributed systems. That definition matters because it tells you that a protocol is not just an encryption scheme. It is a full contract between communicating parties.
In distributed and agent-based systems, that contract must cover four critical properties:
- Confidentiality: Data is readable only by intended recipients.
- Integrity: Data cannot be modified in transit without detection.
- Authentication: Both parties verify each other’s identity before exchanging data.
- Availability: The protocol must remain functional under load, failure, or attack.
Standard TLS addresses confidentiality and server-side authentication well. But it was designed for client-server interactions, not for peer networks where any agent can initiate a session with any other. When you have hundreds of autonomous agents communicating across cloud regions, you need network-layer protocol rules that go well beyond what a single TLS handshake provides.
“Security is not a feature you add to a protocol. It is a property that must be designed into every layer of the communication stack from the start.”
The OSI model gives you seven layers. In practice, most teams only secure layers four and above. Agents operating in decentralized environments need explicit security decisions at the network layer, the session layer, and the application layer. Skipping any one of these creates an attack surface that is easy to miss and hard to detect after the fact.
Centralized vs decentralized security models
Understanding protocols in theory is only part of the story. Practical deployment for distributed and autonomous agent networks means picking the right security architecture.
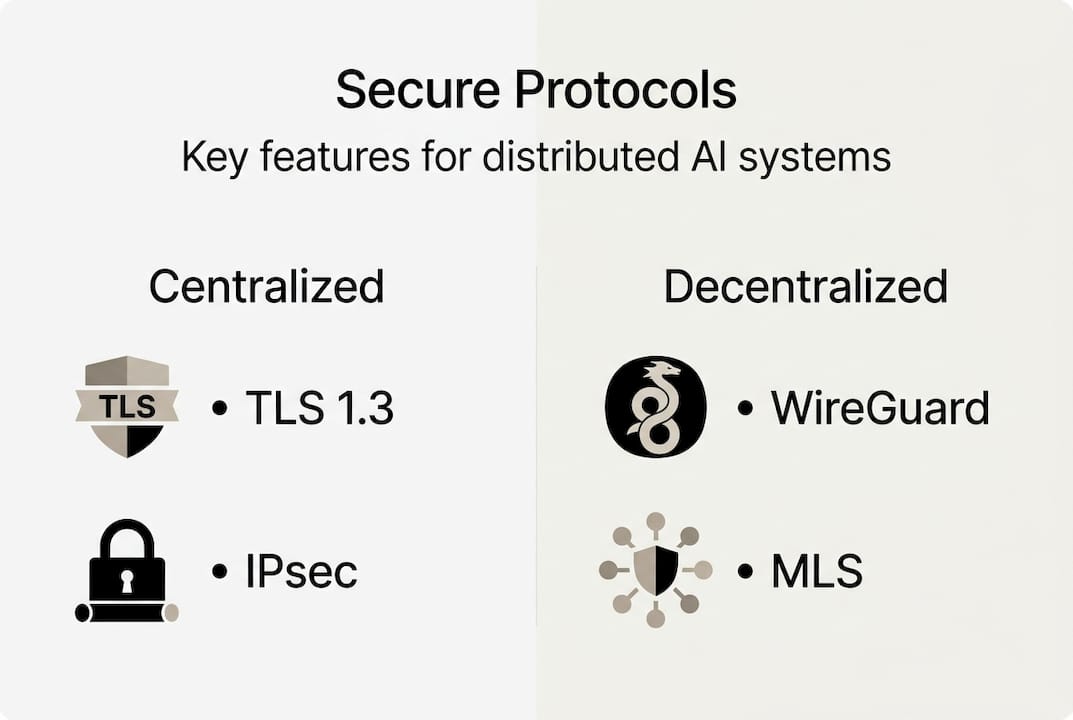
Centralized versus decentralized security breaks down like this: centralized models like TLS and IPsec offer easier key management but introduce a single point of failure. Decentralized models like MLS and WireGuard scale for agent-to-agent communication but require ratcheting and post-compromise security (PCS) to maintain forward secrecy.
| Feature | Centralized (TLS/IPsec) | Decentralized (MLS/WireGuard) |
|---|---|---|
| Key management | Simpler, central CA | Distributed, ratchet-based |
| Failure risk | Single point of compromise | Resilient, no central target |
| Scalability for agents | Limited | High |
| Forward secrecy | Optional | Built-in (WireGuard, MLS) |
| PCS support | No | Yes (MLS) |
For autonomous agent fleets, decentralized models are generally the stronger choice. They eliminate the central broker that attackers love to target. Explore decentralized protocol patterns and zero-trust for AI agents to see how these principles apply in practice.
Key architectural factors to evaluate:
- Forward secrecy (FS): Does compromise of a long-term key expose past sessions?
- Post-compromise security (PCS): Can the system recover security after a key is exposed?
- Key distribution: How are keys rotated across a dynamic agent population?
- Fail-safe behavior: What happens when a node goes offline or a key expires?
Pro Tip: Always evaluate FS and PCS requirements before selecting an architecture. For agent networks where membership changes frequently, a protocol without PCS will leave you exposed after any key compromise event.
Core secure protocols: TLS 1.3, IPsec, WireGuard, mTLS, and MLS
Having mapped out the architectural options, let’s compare the core protocols you actually have to choose from.
TLS 1.3 (RFC 8446) provides confidentiality, integrity, and authentication via a 1-RTT handshake, (EC)DHE key exchange, AEAD ciphers including AES-GCM and ChaCha20-Poly1305, and an HKDF key schedule. It is the baseline for most web and API traffic.
IPsec (RFC 4301) uses AH and ESP headers for IP-layer security. WireGuard, by contrast, uses the Noise protocol framework with fixed cryptographic primitives, delivering high throughput and low latency with a much smaller codebase. mTLS (RFC 8705) extends TLS for mutual authentication, which is essential for securing service mesh east-west traffic. MLS (RFC 9750) enables secure group messaging and dynamic membership, making it a strong fit for agent networks where participants join and leave frequently.
| Protocol | Layer | Key strength | Weakness |
|---|---|---|---|
| TLS 1.3 | Transport | Fast handshake, modern ciphers | Server-auth only by default |
| IPsec | Network | Full IP-layer encryption | Complex config, NAT issues |
| WireGuard | Network | Simple, fast, fixed crypto | UDP only |
| mTLS | Transport | Mutual auth | Cert lifecycle complexity |
| MLS | Application | Group FS and PCS | Newer, fewer implementations |
How to choose:
- Use TLS 1.3 for external API endpoints and client-facing services.
- Use mTLS for internal service mesh communication where mutual auth is required.
- Use WireGuard for P2P agent tunnels where performance matters. See WireGuard for P2P AI for implementation guidance.
- Use IPsec when you need network-layer encryption across existing infrastructure. Review IPsec implementation details before deploying.
- Use MLS when your agent network has dynamic group membership and you need PCS. Pair it with modern cipher suites for maximum coverage.
Pitfalls, limitations, and real-world deployment challenges
Even with the strongest protocols, real-world challenges can introduce new risks. Here’s what you need to watch out for.
The most common failure modes come not from cryptographic weaknesses but from misconfiguration and edge cases: TLS 0-RTT replay vulnerabilities, IPsec NAT traversal problems, WireGuard’s UDP-only operation being blocked by restrictive firewalls, and certificate lifecycle failures in mTLS deployments.
Specific risks by protocol:
- TLS 1.3 0-RTT: Early data can be replayed by an attacker. Disable 0-RTT for any non-idempotent operations.
- IPsec: NAT traversal requires UDP encapsulation (NAT-T). Misconfiguring this is extremely common in cloud deployments.
- WireGuard: It operates over UDP only. Environments with strict firewall rules will block it silently, causing connection failures that are hard to diagnose.
- mTLS: Certificate rotation in dynamic systems is a lifecycle management problem. Expired or revoked certs in a mesh can cause cascading service failures.
- General: Default settings in most protocol implementations favor compatibility over security. Always audit defaults before deploying.
“The most dangerous misconfiguration is the one you don’t know you made. Threat model explicitly, and validate every assumption about your network boundary.”
Review zero-trust implementation tips and agent trust model pitfalls to avoid the most common architectural mistakes.
Pro Tip: Run a protocol audit before production deployment. Check cipher suite negotiation, certificate validity windows, and firewall rules for each protocol in your stack. Automated tooling like testssl.sh or custom health checks in your CI/CD pipeline will catch issues before they reach production.
Zero-trust, blockchain, and the future of agent-to-agent (A2A) security
Resilience is not just about patching problems, but about anticipating the fast-evolving future of secure agent communications.
Zero-trust mandates authentication on every request and is the foundational model for distributed cloud systems per NIST SP 800-207. In practice, this means every packet, every API call, and every agent handshake must be authenticated, regardless of network position. No implicit trust, ever.
Blockchain-based decentralized identifiers (DIDs) and emerging protocols like BlockA2A enable verifiable agent-to-agent communication without relying on a central authority. This is particularly relevant for open agent networks where you cannot control every participant’s infrastructure.
Checklist for future-proof protocol selection:
- Does the protocol support zero-trust by default, requiring auth on every session?
- Does it provide forward secrecy and PCS for long-lived agent networks?
- Can it integrate with decentralized identifiers for verifiable agent identity?
- Does it support dynamic group membership without full re-keying?
- Is the zero-trust model enforced at the protocol level, not just the application layer?
- Can it operate across NAT boundaries and multi-cloud environments without a central broker?
- Is the implementation auditable, with a small, reviewable codebase?
MLS and mTLS with JWT claims are emerging as strong candidates for scalable, verifiable A2A communication. Combined with DIDs, they give you a path to fully decentralized trust without sacrificing auditability.
A practitioner’s perspective: What most guides miss about protocol security
Most protocol security guides focus on cryptographic primitives and compliance checklists. That is useful, but it misses where security actually breaks down in production.
In our experience, security failures in distributed agent systems almost never come from a broken cipher. They come from assumed trust models, overlooked handshake edge cases, and lifecycle mismanagement. A team that correctly implements TLS 1.3 but never rotates certificates, or that deploys mTLS without a revocation strategy, is not secure. It just looks secure.
For open, agent-driven systems, composable protocols and explicit threat modeling matter more than any single “secure” protocol choice. You need to know what your threat model actually is, not what you assume it is. That means documenting every trust boundary, every key lifecycle, and every failure mode before you write a line of configuration.
Continuous validation and observability are as important as initial configuration. Protocols drift. Certificates expire. Firewall rules change. The teams that maintain real security are the ones running field-tested deployment lessons through automated checks continuously, not just at launch. Build observability into your protocol stack from day one.
How Pilot Protocol helps you implement secure communication at scale
If you’re ready to move from theory to resilient systems, Pilot Protocol provides the foundation for secure, scalable agent networks.

Pilot Protocol is built specifically for the challenges covered in this guide. It gives your agents virtual addresses, encrypted tunnels, and NAT traversal out of the box, so you can connect agents across clouds and regions without a central broker. It wraps existing protocols like HTTP, gRPC, and SSH inside its overlay, making it straightforward to integrate with your current stack. Its mutual trust model and persistent addresses align directly with zero-trust implementation with Pilot Protocol, giving you the architectural foundation to enforce authentication at every layer. Start building secure, direct agent communication today.
Frequently asked questions
What is the main difference between TLS 1.3 and mTLS?
TLS 1.3 encrypts traffic and authenticates the server only. mTLS requires both client and server to present certificates, enabling mutual authentication that is critical for service mesh environments.
Why is WireGuard favored for agent networks over IPsec or OpenVPN?
WireGuard delivers faster throughput and lower latency, with benchmarks showing 900+ Mbps and two to four times the speed of OpenVPN, plus a simpler configuration surface that reduces misconfiguration risk.
What are the key risks when deploying secure protocols in distributed AI networks?
The primary risks are misconfigurations, poor key management, NAT and firewall traversal failures, and insufficient handling of TLS 0-RTT replay or protocol downgrade attacks.
How does zero-trust differ from traditional perimeter security?
Zero-trust requires authentication on every individual request, not just at the network perimeter, which eliminates the risk of lateral movement once an attacker is inside your network boundary.
Is blockchain relevant for protocol security in agent communications?
Yes. Blockchain and DIDs enable decentralized, verifiable agent identities and trust relationships, removing the need for a central certificate authority in open agent networks.